Today, BIDAR.ca is proud to be on-site at the Turning AI and Robotics into Measurable Operational Gains event in Markham, Ontario, joining a...
BIDAR.ca Joins “Turning AI and Robotics into Measurable Operational Gains” Here’s a polished blog draft you can use (or adapt) to announce BIDAR.ca’s participation...
🔑 Core Overview These Terms form a legally binding agreement between users and Indeed. By using Indeed’s website, apps, or APIs, you agree to...
Based on Radio Bidar Episode 101 with Hamed Hamedian Guest Introduction In Episode 101 of Radio Bidar, we had the pleasure of hosting Hamed...
The Growth of Business Intelligence The global business intelligence (BI) market is projected to reach $26.5 billion by 2033, highlighting its increasing importance across...
Podcast No. 93 of Radio Bidar Topic: Review of the book The Singularity Is Nearer When We Become One with Artificial Intelligence The Singularity...
Summary of Episode 92 of Radio Bidar Topic: In this session of Radio Bidar, Mostafa Erfani, Technical Director and specialist in Artificial Intelligence and...
Topic: A Look at the Present and Future Predictions of Robotics In episode 89 of Radio Bidar, featuring Mr. Pouyan Asgarian, a Ph.D. student...
Link to join the event: https://venue.electronworkshop.com.au/b/fsm-nxe-7qn-11s
What is ESG Data? ESG Data, standing for Environmental, Social, and Governance, represents the three essential components that companies utilize to assess their...

 The Importance of Startup Communities for the Success of Iranian Entrepreneurs in Canada
The Importance of Startup Communities for the Success of Iranian Entrepreneurs in Canada  Summary of Episode 92 of Radio Bidar – Machine learning Startup
Summary of Episode 92 of Radio Bidar – Machine learning Startup  Episode 89 of Radio Bidar Podcast: A Look at the Present and Future Predictions of Robotics by Pouyan Asgarian
Episode 89 of Radio Bidar Podcast: A Look at the Present and Future Predictions of Robotics by Pouyan Asgarian  BIDAR.ca Live at “Turning AI and Robotics into Measurable Operational Gains”
BIDAR.ca Live at “Turning AI and Robotics into Measurable Operational Gains”  BIDAR on AI & Robotics into measurable operational gain Workshop – Toronto 1st May 2026
BIDAR on AI & Robotics into measurable operational gain Workshop – Toronto 1st May 2026 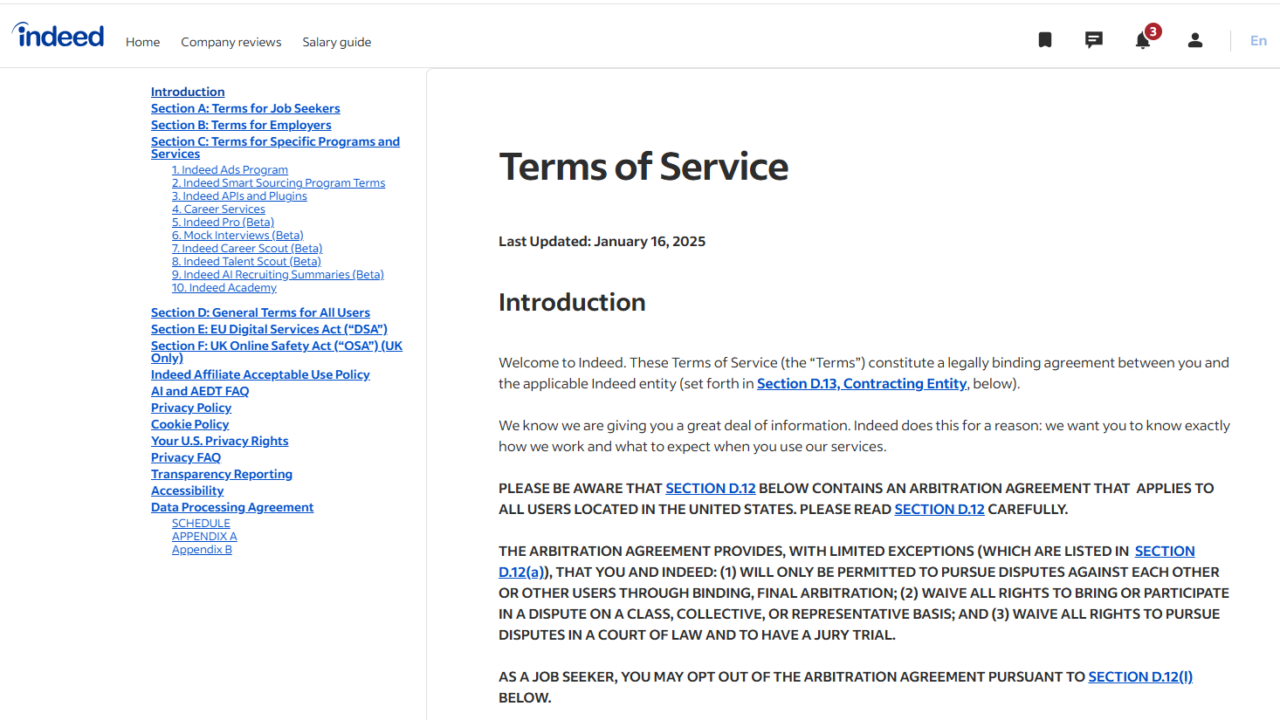 Terms indeed.com Updated January 16, 2025
Terms indeed.com Updated January 16, 2025  The Importance of Startup Communities for the Success of Iranian Entrepreneurs in Canada
The Importance of Startup Communities for the Success of Iranian Entrepreneurs in Canada  Business Intelligence: A Strategic Asset for Modern Companies
Business Intelligence: A Strategic Asset for Modern Companies  BIDAR.ca Live at “Turning AI and Robotics into Measurable Operational Gains”
BIDAR.ca Live at “Turning AI and Robotics into Measurable Operational Gains”  BIDAR on AI & Robotics into measurable operational gain Workshop – Toronto 1st May 2026
BIDAR on AI & Robotics into measurable operational gain Workshop – Toronto 1st May 2026  Terms indeed.com Updated January 16, 2025
Terms indeed.com Updated January 16, 2025  The Importance of Startup Communities for the Success of Iranian Entrepreneurs in Canada
The Importance of Startup Communities for the Success of Iranian Entrepreneurs in Canada  Business Intelligence: A Strategic Asset for Modern Companies
Business Intelligence: A Strategic Asset for Modern Companies  Business Intelligence: A Strategic Asset for Modern Companies
Business Intelligence: A Strategic Asset for Modern Companies  Understanding ESG Data and Reporting
Understanding ESG Data and Reporting  The Crucial Role of Business Intelligence Developers in Empowering Decision-Making
The Crucial Role of Business Intelligence Developers in Empowering Decision-Making 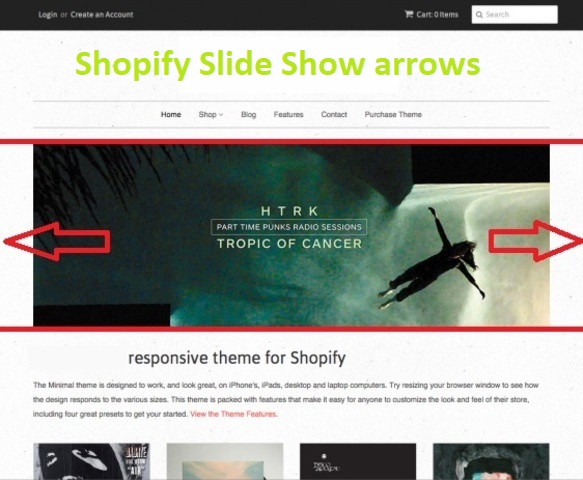 Protected: How to Fix Slideshow Arrows on Shopify Theme Liquid
Protected: How to Fix Slideshow Arrows on Shopify Theme Liquid  BIDAR.ca Live at “Turning AI and Robotics into Measurable Operational Gains”
BIDAR.ca Live at “Turning AI and Robotics into Measurable Operational Gains”  BIDAR on AI & Robotics into measurable operational gain Workshop – Toronto 1st May 2026
BIDAR on AI & Robotics into measurable operational gain Workshop – Toronto 1st May 2026  Terms indeed.com Updated January 16, 2025
Terms indeed.com Updated January 16, 2025  The Importance of Startup Communities for the Success of Iranian Entrepreneurs in Canada
The Importance of Startup Communities for the Success of Iranian Entrepreneurs in Canada  Business Intelligence: A Strategic Asset for Modern Companies
Business Intelligence: A Strategic Asset for Modern Companies  Podcast No. 93 of Radio Bidar Topic: Review of the book The Singularity Is Nearer When We Become One with Artificial Intelligence
Podcast No. 93 of Radio Bidar Topic: Review of the book The Singularity Is Nearer When We Become One with Artificial Intelligence  Summary of Episode 92 of Radio Bidar – Machine learning Startup
Summary of Episode 92 of Radio Bidar – Machine learning Startup  Episode 89 of Radio Bidar Podcast: A Look at the Present and Future Predictions of Robotics by Pouyan Asgarian
Episode 89 of Radio Bidar Podcast: A Look at the Present and Future Predictions of Robotics by Pouyan Asgarian  Software Freedom Day 2024
Software Freedom Day 2024  Understanding ESG Data and Reporting
Understanding ESG Data and Reporting